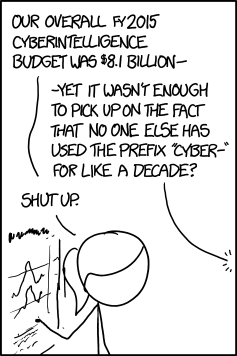
Smart, Is It Not?
via Joe Uchill - writing at Axios, comes this well crafted short read detailing the use of questionable adjectives when announcing cyberattacks, that are - in fact - rarely applicable to the incoident under discussion. Today's Sophisticated Must Read.
'Sophisticated often gets used as a synonym for "our organization shouldn't be blamed for missing this."' - via Joe Uchill - writing at Axios, comes this superb read on the use of adjectives when explaining cybersecurity failures