Black Hat USA 2019, Marie-Sarah Lacharite's 'Breaking Encrypted Databases: Generic Attacks On Range Queries' →
tremendous conference videos on their YouTube Channel
KNOB(d)
via the inimitable Dan Goodin, Security Editor at Ars Technica, comes this troubling blog post detailing the deep flaws in Bluetooth radio communications. Monikered KNOB (Key Negotiation of Bluetooth), the flaw permits interception of data in transit due to forced utilization of weak encryption. Today's MustRead!
"KNOB doesn't require an attacker to have any previously shared secret material or to observe the pairing process of the targeted devices. The exploit is invisible to Bluetooth apps and the operating systems they run on, making the attack almost impossible to detect without highly specialized equipment." - via Dan Goodin, Security Editor at Ars Technica
The Fix Is In: Clodflare's eSNI
Another fix is in the works for one of the more hidden aggravations of internetworking security, the so-called Server Name Indication (SNI) extension debacle. The fix - an Encrypted Server Name Indication has been crafted by Clouflare and evidenced by the service itself - eSNI - is an indication of a Company-Doing-The-Right-Thing and enrypting-all-the-things. Additional work is currently underway targeting a IETF Draft RFC. Simply Outstanding Work, Cloudflare.
Larry Seltzer's 'Data encryption: How To Avoid Common Workarounds'
via the inimitable Larry Seltzer, comes this superlative post over at HPE; in which, Mr. Seltzer details data encryption workarounds, and a method to avoid same. Definately, today's Must Read.
EnclaveDB, The Proposition
via Christian Priebe of Imperial College London, Manuel Costa and Kapil Vaswani both from Microsoft Research, comes a tour dé force of database security, ostensibly monikered EnclaveDB (published this past May 2018, in the Proceedings of the 39th IEEE Symposium on Security & Privacy, in co-operation with the International Association for Cryptologic Research). The interesting functionality descibed in the trio's paper - pursuant to a secure database (if there possibly could be such a thing) is not the security of data in-motion or at-rest, but the addition of encrypted in-memory data. More here...
Telegram Updated, Amidst Kremlin Capers, Apple Angst →
News from over the weekend - via 9to5Mac writer Michael Potuck, focusing on Telegram; of which, the encrypted messaging iOS app has been permitted to publish the latest update to their bits - via Apple Inc. (Nasdaq: AAPL) iTunes App Store. This, despite the declaration of illegality by Kremlin Apparatchiki. Today's Must Read.
Hardware Envelope, A Secure Conveyance →
via Samuel H. Moore, writing at the IEEE's Spectrum Magazine, comes word of the 'Unhackable Envelope'. The Fraunhofer team (developers of the Unhackable Envelope) comprised of Vincent Immler - Fraunhofer Institute for Applied and Integrated Security (AISEC), Martin König - Fraunhofer Research Institution for Microsystems and Solid State Technologies (EMFT), Johannes Obermaier - Fraunhofer Institute for Applied and Integrated Security (AISEC), Matthias Hiller - Fraunhofer Institute for Applied and Integrated Security (AISEC) and Georg Sigl - Fraunhofer Institute for Applied and Integrated Security (AISEC) & Technical University of Munich (TUM) appeared at the IEEE International Symposium on Hardware Oriented Security and Trust in Washington, D.C. last week. Additionally, the group's paper 'B-TREPID: Batteryless Tamper-Resistant Envelope with a PUF and Integrity Detection' won the 2018 Best Paper Award at the confrenece (Kudo's are certainly in order!).
Ray Ozzie Points His Magic Wand At Mobile Encryption →
Ray Ozzie's (the former CTO of Microsoft Corporation (Masdaq: MSFT) that created Lotus Notes...) patented encryption plan is clearly not indicative of a tenable solution to the encryption problems governement agencies, and vendors like (Nasdaq: AAPL) are grapplig with like two behemoth Olympic wrestlers on a greased floor. In answer to this rigamarole comes in the form of a particularly interesting post hand-crafted by the inimitable Dan Goodin, at ArsTechnica, in which, the Good Mr.Goodin tells all. Today's MustRead. 20180506 Update: Read El Reg's Thomas Claburn's take on the Ray Ozzie crypto-solution, such as it is...
New S3 Encryption Feature, Is Amazon's Encryption Move Enough? →
You be the judge... Essentially, all are targeted at data-and-objects-at-rest, rather than in-motion (except, perhaps the new cross-region replication feature with KMS).
Regardless, all of the annouced new features are welcome (in my currently rather jaded opinion). Now, if we can just overcome human error (not to mention blatant developer and data-owner lack-of-attention-to-detail, read about that here)...
- Default Encryption – You can now mandate that all objects in a bucket must be stored in encrypted form without having to construct a bucket policy that rejects objects that are not encrypted.
- Permission Checks – The S3 Console now displays a prominent indicator next to each S3 bucket that is publicly accessible.
- Cross-Region Replication ACL Overwrite – When you replicate objects across AWS accounts, you can now specify that the object gets a new ACL that gives full access to the destination account.
- Cross-Region Replication with KMS – You can now replicate objects that are encrypted with keys that are managed by AWS Key Management Service (KMS).
- Detailed Inventory Report – The S3 Inventory report now includes the encryption status of each object. The report itself can also be encrypted. - via Jeff Barr, writing at the AWS Blog
And, thanks for the H/T go out to Trey Blalock over at rapidly growing Firewall Consultants!
Basic Encryption, In Small(ish) Words →
Ed Felten, Ph.D., has written a superb encryption primer - specifically targeting the politicians and policy wonks amongst us - in it's utility of small words. We really like those small words... H/T
Android, The Weakening →
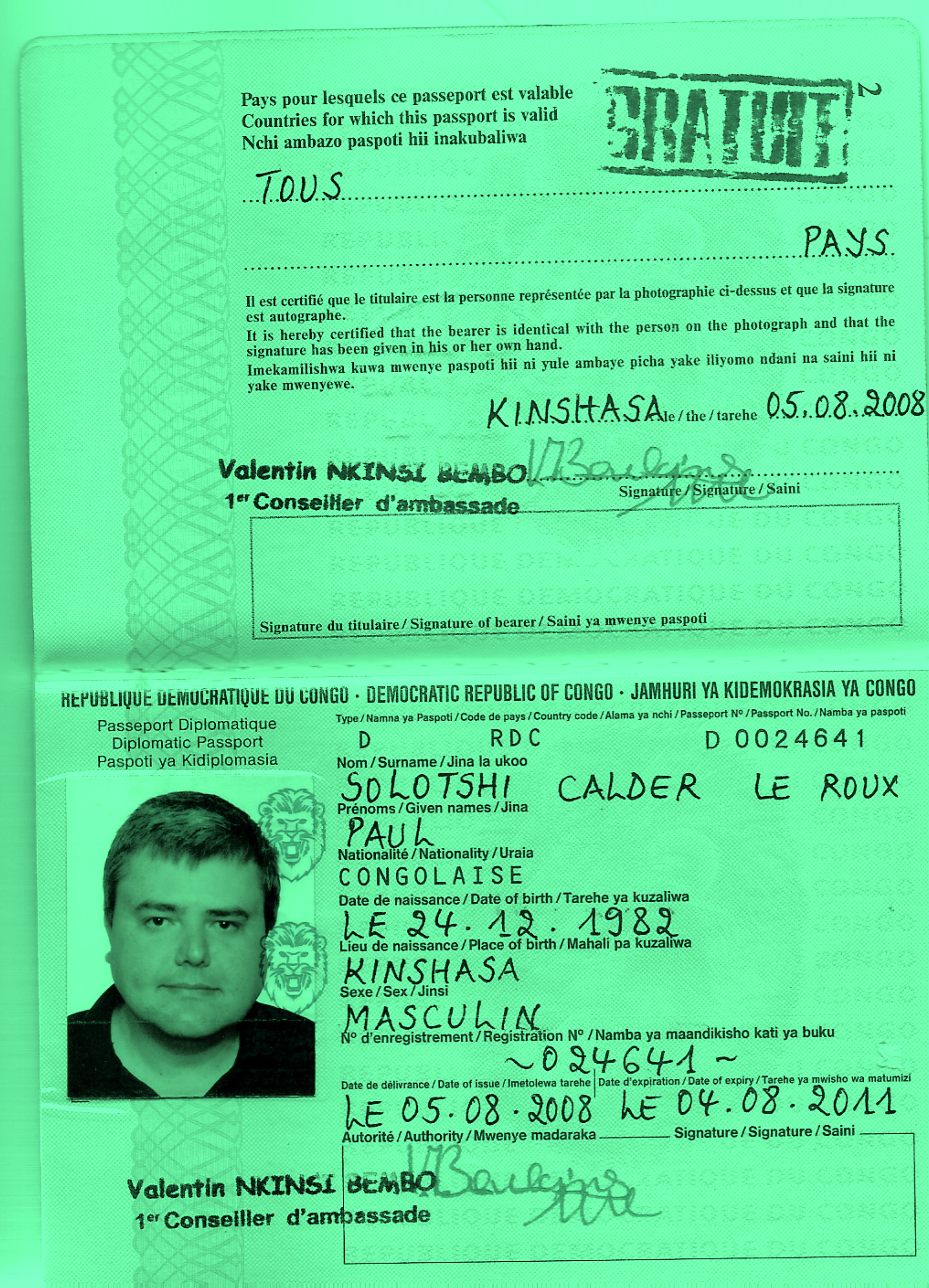
Mastermind, The Paul Le Roux Saga
via Firewall Consultants' Trey Blalock, comes this superb telling of the Paul Le Roux story, written by Evan Ratliff, and published by The Atavist Magazine. Mr. Le Roux also happens to be the man behind TrueCrypt... Hat Tip to Mr. Blalock for this tale of intrigue.
Editors: Katia Bachko, Joel Lovell, Additional reporting: Natalie Lampert, Designer: Thomas Rhiel, Fact checkers: Queen Arsem-O’Malley, Riley Blanton, Research: Aurora Almendral, Daniel Estrin, Copy editor: Sean Cooper, Trailer: Paul Kamuf - credits via The Atavist Magazine
USENIX Announces ENIGMA 2017 →
USENIX’s Enigma Conference is slated for January 30th through February 1st, 2017 at the Oakland, CA Marriott City Center. David Brumley and Parisa Tabriz also reprise their roles as Program Co-Chairs. Most certainly a Must Attend Conference in 2017.
DANE, Huque's Take →
Verisign Principal Research Scientist Shumon Huque, discusses the merits and functionality of DANE (DNS-based Authentication of Named Entities) on CircleID. If you read anything today about DNS, make sure you take a modicum of your precious moments to examine Shumon's outstanding post at CircleID.
Prevent HSTS Tracking →
The eponymous Martin Brinkmann, writing at his gHacks site, details the method used to disable the HTTP Strict Transport Security tracking 'feature' in browsers (specifically, in this case, within Mozilla's Firefox browser. Outstanding.
Google Disables SSL and RC4, Better Late Than Never →
Adam Langley posts good news... Google Inc. (NasdaqGS: GOOG) has finally made the move, and is in the process of disabling SSL v3 (obsoleted 16 years ago) and RC4.
SSLv3 has been obsolete for over 16 years and is so full of known problems that the IETF has decided that it must no longer be used. RC4 is a 28 year old cipher that has done remarkably well, but is now the subject of multiple attacks at security conferences. The IETF has decided that RC4 also warrants a statement that it too must no longer be used. - via Adam Langley writing at the Google Online Security blog.
Encryption, The Trick →
Quite likely one of the best articles on the problematic world of quantum encryption, written by Natalie Wolchover (published in Quanta Magazine) managed to bubble up through the jetsam of our collective interwebs yesterday. Today's Must Read.