Seven Xen Itch
News, via Dan Goodin, writing at Ars Technica, details a seven year old, pernicious bug in Xen virtualiztion wares. In which, users can exploit the bug to breakout of their local machines, thence into the underlying hypervisor layer. FYI - One high profile customer of the Xen Hypervisor is Amazon Web Services. Time to Patch, eh?
"Admittedly this is subtle bug, because there is no buggy code that could be spotted immediately. The bug emerges only if one looks at a bigger picture of logic flows (compare also QSB #09 for a somehow similar situation). On the other hand, it is really shocking that such a bug has been lurking in the core of the hypervisor for so many years. In our opinion the Xen project should rethink their coding guidelines and try to come up with practices and perhaps additional mechanisms that would not let similar flaws to plague the hypervisor ever again (assert-like mechanisms perhaps?). Otherwise the whole project makes no sense, at least to those who would like to use Xen for security-sensitive work." - via Dan Goodin, writing at Ars Technica.
Sunday Security Maxim
Accountability Maxim #1: Organizations that talk a lot about holding people accountable for security are talking about mindless retaliation, not a sophisticated approach to motivating good security practices by trying to understand human and organizational psychology, and the realities of the workplace. Compiled by Roger G. Johnston, Ph.D., CPP, Argonne National Laboratory
Saturday Security Maxim
Michener’s Maxim: We are never prepared for what we expect. Comment: From a quote by author James Michener (1907-1997). As an example, consider Hurricane Katrina. Compiled by Roger G. Johnston, Ph.D., CPP, Argonne National Laboratory
PhoneBoy Speaks, Smartphone Risks →
Dameon Abernathy-Welch, a Security Architect for Check Point Software Technologies, C-List Infosec Celebrity and widely known as PhoneBoy, publishes a typically erudite podcast. In this episode, PhoneBoy presents his thoughts on the risk to the enterprise (this time cuased by the enterprises' management), with the use of ubiquitous 'smartphones'. Listen here.
Herzog, The Truth About Vulnerability Scanners →
Superlative post, well-crafted by the eponymous Pete Herzog (writing at Norses' [Darkmatters), elucidating the truth of vulnerability scanners. Today's Must Read.
NirSoft's AV List o' Shame
Nir Sofer's List of Shame, The Anti-Virus Edition. FYI: We happily make use of Nir's tools and recommend them highly. Enjoy
Doudna's CRISPR Cas9
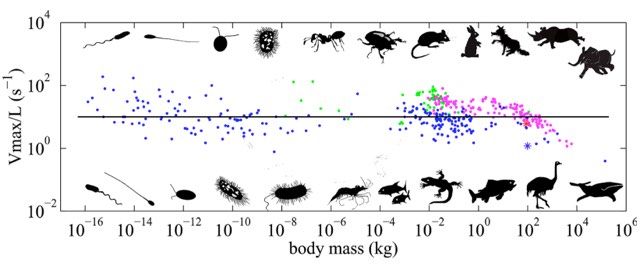
Kottke, Laws of Scaling, Speed of Animals
Absolutely fascinating post over at Jason Kottke's Kottke.org site, illustrating the laws of scaling (in this case body size) and the speed of animals; clearly there are correllations to computational activity.
Sunday Security Maxim
Galileo’s Maxim: The more important the assets being guarded, or the more vulnerable the security program, the less willing its security managers will be to hear about vulnerabilities. Comment: The name of this maxim comes from the 1633 Inquisition where Church officials refused to look into Galileo’s telescope out of fear of what they might see. Compiled by Roger G. Johnston, Ph.D., CPP, Argonne National Laboratory
Saturday Security Maxim
Thursday Maxim: Organizations and security managers will tend to automatically invoke irrational or fanciful reasons for claiming that they are immune to any postulated or demonstrated attack. Comments: So named because if the attack or vulnerability was demonstrated on a Tuesday, it won’t be viewed as applicable on Thursday. Our favorite example of this maxim is when we made a video showing how to use GPS spoofing to hijack a truck that uses GPS tracking. In that video, the GPS antenna was shown attached to the side of the truck so that it could be easily seen on the video. After viewing the video, one security manager said it was all very interesting, but not relevant for their operations because their trucks had the antenna on the roof. Compiled by Roger G. Johnston, Ph.D., CPP, Argonne National Laboratory
Limits of Computation →
John Pavlus, writing at Quanta Magazine regales us with the story of a 'Solution That Doesn't Exist'.
Yet in a paper presented at the ACM Symposium on Theory of Computing, two researchers from the Massachusetts Institute of Technology put forth a mathematical proof that the current best algorithm was “optimal” — in other words, that finding a more efficient way to compute edit distance was mathematically impossible. The Boston Globe celebrated the hometown researchers’ achievement with a headline that read “For 40 Years, Computer Scientists Looked for a Solution That Doesn’t Exist.”
Underwhelming Overengineering →
Writing at the IEEE's Spectrum Magazine, Robert N. Charette and Joshua J. Romero have detailed the Overcomplexifying and Underdelivering model prevalent in massive-fail software implementations and deployments. Todays Death March Must Read.
As hard as it is to build IT systems in the first place, it’s arguably even more difficult to maintain them properly over time. In many government agencies, decades of neglect have resulted in a tangled mess of poorly understood and poorly implemented systems that limit operational effectiveness and efficiency. In the past decade, we’ve seen numerous attempts to combine the functionality of such legacy systems into a single modern replacement system. - Via Robert N. Charette and Joshua J. Romero writing at the **IEEE Spectrum Magazine.