IPv6, The Fragmentation Chronicles →
or, How I learned to Relax and Trust in Large-Addressing-Schemes-That-Should-Have-Been-Designed-To-Be-Free-From-Worry...
IoT'd →
New, oddly optimistic screed - detailing the belief that ISP's should mitigate/remediate bad IoTbehaviors - has surfaced at Wired. You be the judge.
Attack Map →
The newly released DDoS Attack Map tool from Jigsaw. Recommended for the minimal eye candy, and apparent accuracy...
IoT'd →
News, via the inimitable Dan Goodin, writing at Ars Technica, of newly released DDoS source code leveraging IoT devices. Beware that new Bluetooth cuddly stuffed bear, it's a killer (and let's ignore the rabbit for now)...
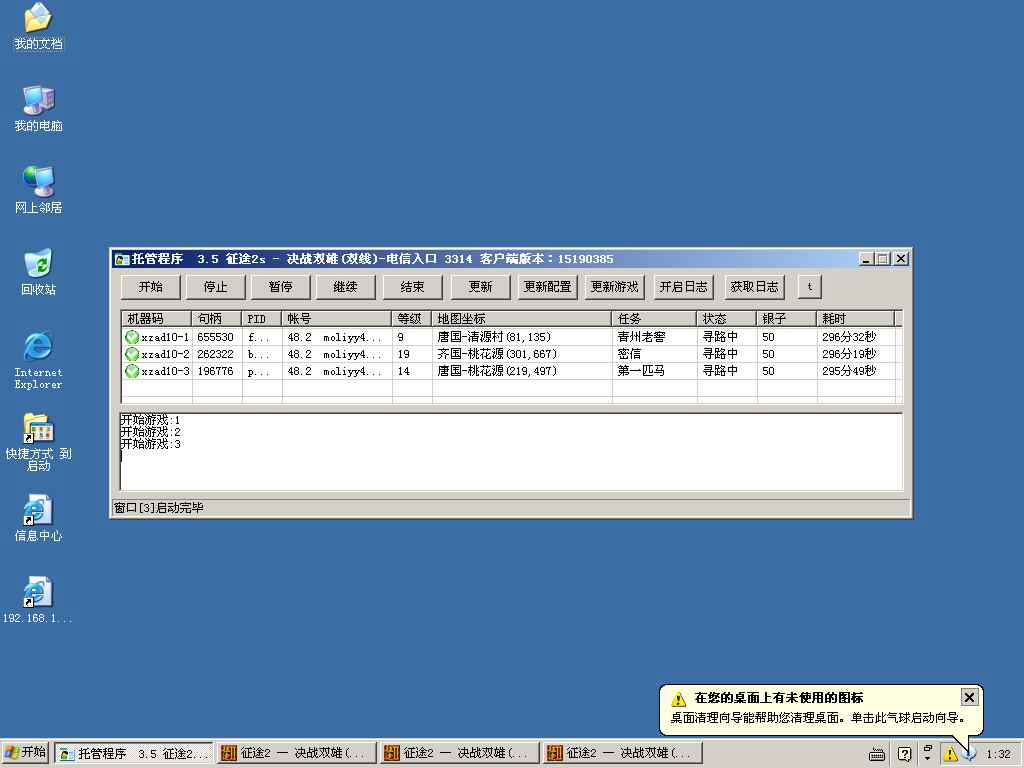
VNC Roulette... →
Backdoor In Motion →
Bernardo Rodrigues, writing at his blog W00tSec, publishes a superlative screed comprised of excrutiating well wrought research and proof thereto - of the backdoors in-built by cable modem manufacturers, Todays' Must Read. Enjoy.
Network Security, It's About The Peoples... →
In a well crafted post at CircleID; in which, security design in the network realm is explored, Burt Kaliski proposes a re-focusing on the rationale of secure system design.
IP Spoof, Stoppable?
Andrei Robachevsky - writing at CircleID, explores the potential to halt IP Spoofing. Today's MustRead (along with the ISOC whitepaper referred to in the original post).
Mitigating the reflection component of the attack is one way of addressing the problem. As reported by the OpenResolver project, in the last two years the amount of open DNS resolvers has dropped almost by half — from 29M to 15M. However, there are other types of amplifying reflectors — NTP and SSDP are among them, and even TCP-based servers (like web servers, or ftp servers) can reflect and amplify traffic. Andrei Robachevsky - writing at CircleID
McRee's Visualizing Network Data With Network Data
Russ McRee's well-wrought piece published on his highly respected HolisticInfosec site, within his toolsmith column (both on his site and formerly in the ISSA Magazine) provides a tour-de-force primer on utilizing the R Development Environment. R in this case, is bent to Russ's will to accurately depict (of course) network data (in this case generated by (and in Russ's words) - "network traffic packet capture specific to malware called Win32/Sirefef or ZeroAccess that uses stealth to hide its presence on victim systems". Today's Must Read.
Microsoft WiFi Sense BS Meter Approaching Warning Levels
Simply speechless at the shenanigans in Redmond, what with the monkeying with WiFi key sharing, and all. Let's see what other sources have to say about [WiFi Sense][1].
Brian Krebs, from Krebs on Security, speaks the truth with obious clarity:
"This brilliant new feature, which Microsoft has dubbed Wi-Fi Sense, doesn’t share your WiFi network password per se — it shares an encrypted version of that password. But it does allow anyone in your Skype or Outlook or Hotmail contacts lists to waltz onto your Wi-Fi network — should they ever wander within range of it or visit your home (or hop onto it secretly from hundreds of yards away with a good ‘ole cantenna!)." - via Brian Krebs at Krebs on Security
And this from the El Reg's Simon Rockman:
Wi-Fi Sense doesn’t reveal the plaintext password to your family, friends, acquaintances, and the chap at the takeaway who's an Outlook.com contact, but it does allow them, if they are also running Wi-Fi Sense, to log in to your Wi-Fi. The password must be stored centrally by Microsoft, and is copied to a device for it to work; Microsoft just tries to stop you looking at it. How successful that will be isn't yet known. - via Simon Rockman at El Reg